While call center software enables a company to improve customer experience with flexible interactions and self-service, call centers are a prime target for scammers. These fraudulent attacks can damage a company’s finances, reputation, and future business opportunities.
But how can you identify fraudulent actors and protect your call center from these attacks?
This article will outline call center fraud in depth, explaining what it is, the most common types, the consequences of fraud, how to identify it, and how to protect against it.
- What is Call Center Fraud?
- Types of Call Center Fraud
- Consequences
- How to Identify
- How to Prevent
- Protect Your Company
What is Call Center Fraud?
Call center fraud is when a hacker contacts a call center under a fake identity in order to gain access to private data or account controls.
Hackers typically call in with fraudulent or stolen information–like a customer’s or employee’s name, personal information, or credit card number. They aim to convince call center staff to grant them access to the real user’s account, controls, or information. Alternatively, hackers may seek to take action on behalf of the real customer or employee, such as ordering products with the customer’s credit card information, altering login data, or even transferring funds.
With the employee’s or customer’s controls, the fraudster can take dangerous action:
- Access personal information about users and customers–including bank accounts, credit card information, identity data, and more
- Drain account funds
- Download customer records, conversations, transcripts
- Use authority to order debit cards, products, and expensive materials
- Transfer funds to their own account
- Change account information to lock users out, and more
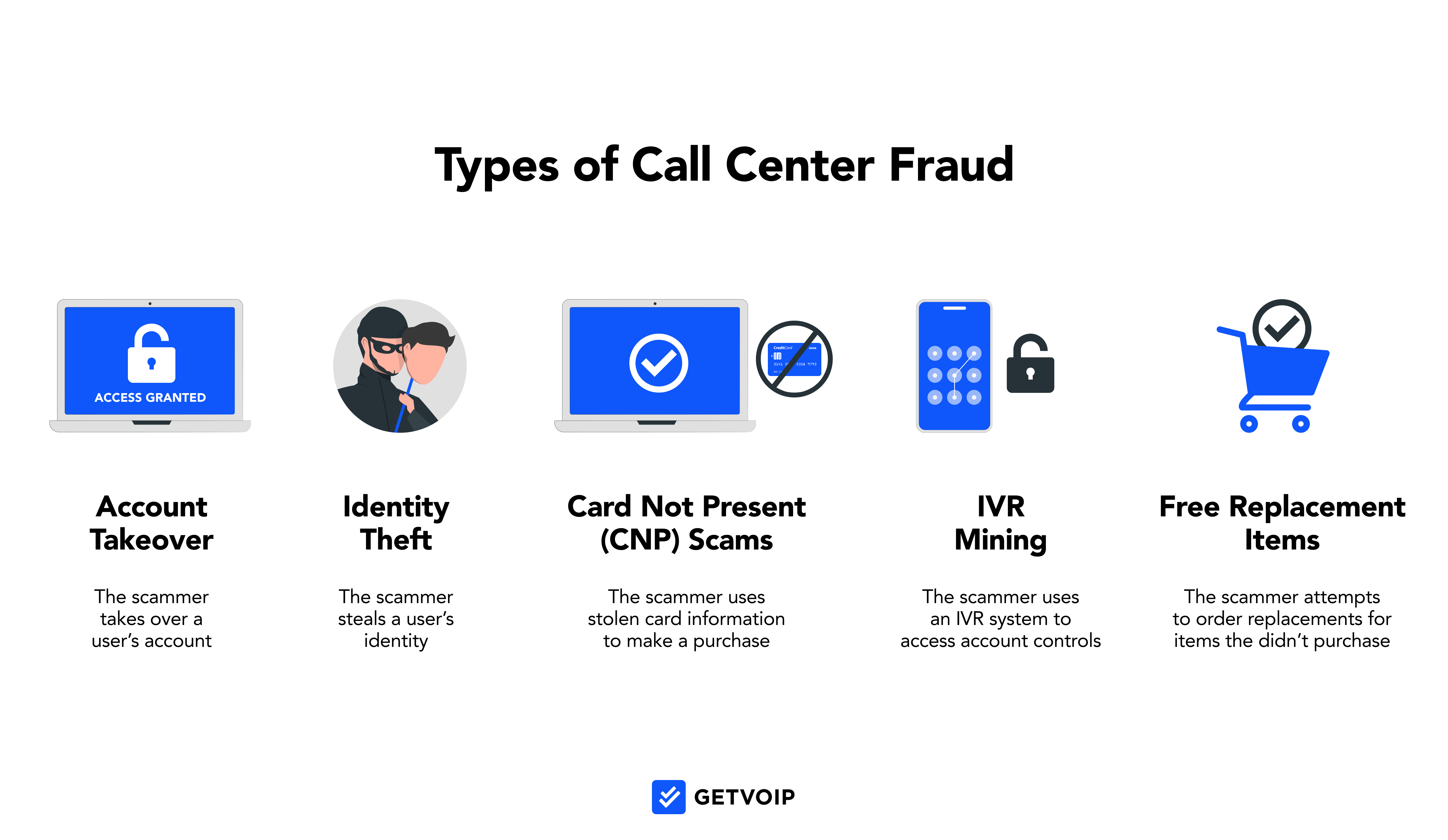
Types of Call Center Fraud
These are 5 most common types of call center fraud:
All of these call center fraud activities involve spoofing or phishing.
Spoofing is when a scammer tries to impersonate someone’s identity, such as a call center user.
Phishing is when a scammer attempts to steal information–such as a user’s billing information, profile details, or login credentials–usually through a fraudulent business email or web link, sent under the guise of a trusted company.
1. Account Takeover
Account takeover is when a scammer attempts to access a user’s account and lock the real user out.
The fraudster typically contacts a call center agent and presents personal identity information (PII) stolen from the real user–the three most common forms of PII being the user’s name, social security number, and birth date. They use this information to spoof the call center agent into granting them account access, before locking out the real user via several methods: changing passwords, PIN numbers, or contact information.
Finally, the scammer attempts to order products, transfer money, take out loans, drain account funds, or access sensitive data like billing information and private records.
2. Identity Theft
Identity theft is when a scammer contacts a call center under an employee’s or customer’s identity, using their PII in an attempt to gain access to their controls. In 2022 identity theft accounted for 21% of consumer complaints, making it one of the most common types of call center fraud.
Sometimes, the fraudster may gain highly personal information–such as the user’s driver’s license number or medical record number–making it easier for them to impersonate the real user and trick the agent into granting account access, controls, or authority. The spoofer may have gathered this PII through a stolen device, personal contact with the user, a stolen identification card, or hacked WiFi.
3. Card Not Present (CNP) Fraud
Card not present (CNP) fraud is when the fraudster makes a transaction without physically presenting the payment card to the vendor.
The scammer often uses a stolen debit card, or stolen card information, to order a vendor’s products and services over the phone, via IVR, or online. Since the transaction is remote, the scammers avoid having to visually verify their identity. CNP fraud is becoming especially common in recent years, as a 2021 Pulse study found that one-third of debit transactions are made remotely. Thankfully, advanced chargeback technology enables an 87% recovery rate once users or call centers identify a fraudulent CNP transaction.
4. IVR Fraud (IVR Mining)
Interactive voice response (IVR) fraud is when hackers contact a call center IVR system in an attempt to gain information, access the customer’s account, or change account credentials.
Unlike live agents, IVR systems verify inbound caller identities via mechanized technology and routines, which usually include passwords, PIN codes, or other knowledge-based authentication processes. Scam calls access these self-service IVR menus–sometimes in bulk via auto dialing technology–to phish customer data like PINs and account numbers, or order replacement products or debit cards.
5. Attempt to Receive Free Replacement Items
Scammers impersonate a vendor’s legitimate customers and request replacement products or a refund in order to receive free materials or money, often claiming their order was damaged or undelivered.
This type of call center fraudster usually requests to send the replacement products or funds to a new address, bank account, or email address.
Consequences of Call Center Fraud
Call center exploitation causes a variety of consequences for the customer, company, and industry.
- Financial Damage and Product Loss
- Reputational Damage
- Compromised Data
- Loss of Company Value
- Fines
- Business Interruption
Financial Damage and Product Loss
When successful, call center fraud costs companies a lot of money. An affected company often loses products and materials, cash funds, and often must compensate any damages their customers face due to the call center’s negligence.
In fact, a 2020 ACFE report found that the median loss for a small-to-medium-sized business affected by fraud is $125,000. Unfortunately, 54% of affected organizations were unable to get any of this money back after the attack.
Reputational Damage
When a company suffers from a cyberattack or fraudulent actor, they lose the trust of not only the affected customers but all customers who hear of the attack.
Especially for companies that handle sensitive information, like healthcare and financial institutions, an image of poor security can damage a company’s reputation. This damaged reputation can cost a company a substantial number of future business opportunities.
Compromised Data
When a hacker manipulates an IVR system, call center agent, or gains access to a private call center account, the hacker gains access to large amounts of customer data. This is called a data breach.
Call center hackers can access a user’s conversation histories, sent messages and emails, call records, detailed customer profiles with personal data and purchase history, medical records, and billing information. If stolen, this information can lead to financial and reputational damage for a call center’s customers.
Loss of Company Value
A fraud attack may suggest weakness in a company’s overall functionality, additionally warning about the risk of future losses. This, along with the damaged reputation and reduced employee morale a company suffers from a fraud attack, can lower the victim company’s business valuation.
Fines
In some cases, the call center company exploited by fraud may receive regulatory fines. This is more likely if the call center neglected security regulations, such as utilizing two-factor authentication or knowledge base authentication (KBA) questions.
Business Interruption
Once detected and confirmed, call center fraud disrupts a business’ processes in several ways.
An affected company often must put business processes on hold. The company must identify the scam’s source, hire new employees for this research if necessary, research and notify all affected parties, determine the extent of the damage, and rework relations and reimbursement with the affected customers.
How to Identify Call Center Fraud
While some scammers can be difficult to detect–especially if they’ve stolen a user’s PII–it’s helpful for call center agents to remain aware of common fraud indicators.
Call center agents can suspect call center fraud based on these signs:
- Has difficulty answering KBA questions: If the inbound caller pauses before answering an authentication question, or if they’re unable to answer one
- Cannot perform authentication processes: If the caller cannot perform two-factor authentication, answer security questions, participate in voice biometrics, or complete facial identification, this suggests suspicious behavior
- Attempts to avoid authentication processes: If the caller attempts to avoid authentication processes–or if they become emotional or angry when asked to do so
- Builds rapport with a particular agent: If a caller asks to speak with a particular agent, or places special effort into building rapport with one agent, this may indicate that the caller is trying to exploit the agent
- History of failed login or account-access attempts: If the account history shows several failed login attempts, this may suggest a fraud attempt with several recent unsuccessful tries
- Caller’s information doesn’t match the profile’s records: If the inbound call or email comes from a number or address that isn’t part of the customer’s profile, the agent should take additional steps to verify their identity
- Cross-channel behavior seems unusual: If the caller contacts your via a channel they don’t normally use–or at an abnormal time of day–this atypical pattern may indicate a spoofer
- Requests to change or utilize a new contact address: If the caller requests to change their address or phone number–or send products or authentication to a new address–the agent should take additional steps to verify the user’s identity
How to Prevent Call Center Fraud
Although fraudulent attacks can be costly, there are several steps you can take to protect your call center and prepare your agents.
Here are the top call center fraud-prevention strategies:
- Integrate fraud prevention in employee training: Pindrop reports that 1 in 2,200 live-agent calls are fraudulent, making it necessary to train call center agents about fraud prevalence, risks, warning signs, and prevention methods. Call center employee training should teach agents to spot red flags and remain well-versed in authentication protocols.
- Utilize multi-factor authentication (2FA): Multi-factor authentication requires a user to verify their identity through multiple touchpoints or devices before accessing an app. For example, after the user successfully enters their password, the app may prompt them to verify with a system code via text, email, or an authenticator app. 2FA makes it much more difficult for a scammer to impersonate someone and integrates well with IVR systems.
- Utilize knowledge base authentication (KBA) questions: Knowledge base authentication questions are an authentication method that verifies a user’s identity by asking them personal questions that they answered upon initial sign-up. KBA questions are ones that a spoofer would be unlikely to know, such as “Where did you go to elementary school?” or “What was your first pet’s name?” Implement KBA questions in authentication protocols with a virtual agent, IVR, app, or live agent.
- Integrate security-based applications: Call center applications integrate with security-focused applications exclusively geared toward strengthening your contact center’s defenses. For example, Adaptive Shield monitors users and flags problematic user behavior, while DoControl provides end-to-end visibility for all call center users.
- Implement protocols for sensitive transactions and data: Some call center as a service (CCaaS) applications enable you to flag transactions for large funds, or interactions including highly personal information. Set the CCaaS system to add an additional authentication protocol or ping a supervisor in these sensitive cases.
- Employee restrictions: Assign each user’s access to app controls in your CCaaS app’s supervisor dashboard, restricting controls based on each user’s role or seniority level. This can help prevent untrained users from handling large transactions, processing refunds, or changing account information.
- Encrypt all calls and texts: Many VoIP phone system providers offer automatic encryption of all data, which means that only users with the encryption key can access the information.
Protect Your Company Against Call Center Fraud
If you want to protect your company against fraudulent activity, the best place to start is with your call center. In fact, Pindrop reports that 61% of fraud can be traced back to a company’s call center.
Thankfully, there are many technologies and strategies you can implement to protect against call center fraud.



