With teams increasingly scattered across the globe, we have come to rely more heavily on virtual collaboration for (the sake of) workplace communication. But while these systems are often advanced and capable of pulling off most work-related tasks, whiteboarding, messaging, calls, group chats, and smaller workplace brainstorming rooms - they are not entirely foolproof.
Social engineering, meaning hackers gaining access to sometimes sensitive calls, messages, and group chats - because they are let in by an employee fooled by a link they assumed came from their internal IT department.
One, but certainly not the only solution to this potential threat is end-to-end encryption, or (E2EE), which RingCentral says it will soon use to fully secure messaging, video, and phone communications.
Essentially: by adding the function, RingCentral plans to encrypt data from each endpoint (both the sender and receiver), effectively establishing encryption keys without human interaction. Having not announced a date for a full-scale launch, E2EE is, however; available in closed beta for select customers of the MVP platform, which reached over five million paid users earlier this year.
The FULL functionality will likely become available in early 2023.
You may recall that RingCentral launched end-to-end encryption earlier this year for its video conferencing solutions. That same experience, it says, is making its way to the firm's business phone and team messaging solutions.
The RC Approach to Phone/Video Encryption
Michael Armer is Chief Information Security Officer at RingCentral and recently wrote a blog post addressing the newest product-line enhancer, noting:
“People exchange millions of calls and messages a day on RingCentral’s platform. With our new E2EE - we are extending enterprise-grade privacy and security controls for our customers, giving them the freedom: to have confidential conversations across any mode.”
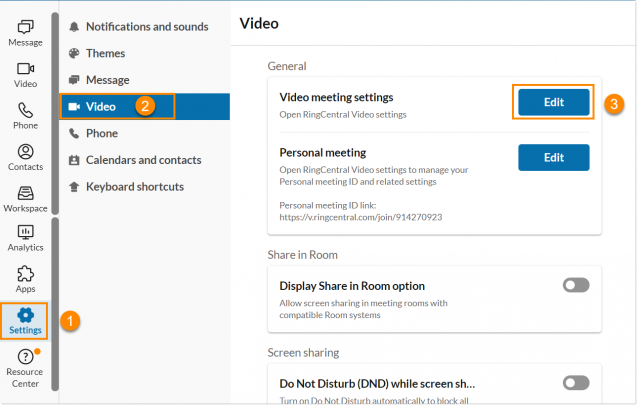
And this holds a lot of weight, especially given what MVP platform users will gain from the function. As of the launch of the closed beta, users can: Enable end-to-end encryption on/off at the organizational level. This is, of course, reserved for someone like a Chief IT Officer or someone with a comparable title.
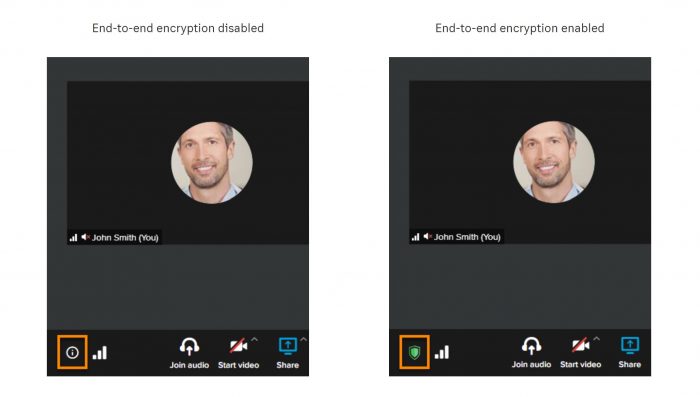 RingCentral End-to-end encryption
RingCentral End-to-end encryption
It will be available for 1:1 calls and can support large groups when it rolls out, as well as extend support softphones, both desktop, and mobile apps. And if the call starts as a non-encrypted one for any reason, users can turn it into a fully-encrypted call with the press of a button.
The same goes for individuals leveraging video meetings. There are some restrictions, though, such as those placed on call recordings; if a guest (is not) signed into a RingCentral account, callers from PSTNs, and callers from traditional phones.
For RC Messaging, Relatively the Same Story
Via MVP messaging, IT admin can still turn on/off at the organizational level, and they gain access to management from the RingCentral desktop app.
Much like calling, there is support for softphones, both desktop, and mobile apps. One of (the most) principal differences is that there is a limit on the number of folks allowed in an encrypted chat. That number is 50 participants. According to RC, the unavailable functionalities are:
- Sending GIFs
- Code snippets
- Third-party apps
- Notification previews
- Sharing team disabled
- Creating tasks, events, notes
- Guests (external users/email addresses) cannot join E2EE team chats
Some, Hesitant to Add End-to-End Encryption
Market leaders like Slack remain hesitant to offer end-to-end encryption and (still) do not offer the functionality.
This is thanks, in large, to executives at large enterprises who wish to retain "complete" visibility into workplace communications. Otavio Freire is President, CTO, and Co-Founder of SafeGuard Cyber, and he said a lot to say about the matter in a blog post.
He sounded the alarm that not extending full encryption could have devastating consequences for users of the Slack platform, writing:
"A data breach affecting Slack could have disastrous consequences for its users. It’s happened before, and there’s every possibility it could happen again. Furthermore, if confidential business data subject to compliance regulations are among the stolen information, the liability will fall on the organization that owns the data."
Fortunately, Slack (does) extend HTTPS encryption, DLP integrations, and its version of Enterprise Key Management (EKM) - hoping to further secure sensitive user/customer data.

Others, including Zoom, have introduced end-to-end encryption to its platform, looking to combat things like Zoombombing - which is what it sounds like, it is.
Microsoft and its popular Teams offering also extend end-to-end encryption, along with (the likes of) lesser-known players like Wire, which touts itself as the most secure messaging platform. It primarily works with government and non-governmental organizations helping secure sensitive information via end-to-end encryption.
Zero Trust and Education, still Key Tools
RingCentral's move: while not unique, does give it some more clout amongst its competitors, even those like Webex, which does extend end-to-end encryption to all users. It is not merely enough to offer full encryption, and as I say often - education is another way to mitigate and that could help protect against the threat of unwanted intrusion.
I sat down with RingCentral's head of security last year, around this same time, actually, and she told me as much during our time together, noting - that she's a big fan of zero-trust security architecture.
As I wrote then: Zero-trust security means that one cannot access a company network unless the device is deemed suitable through a series of protocols that happen behind the scenes. Typically the end-user is unaware of the process, but it can work to ensure the device is safe to handle sensitive and often priceless company data.
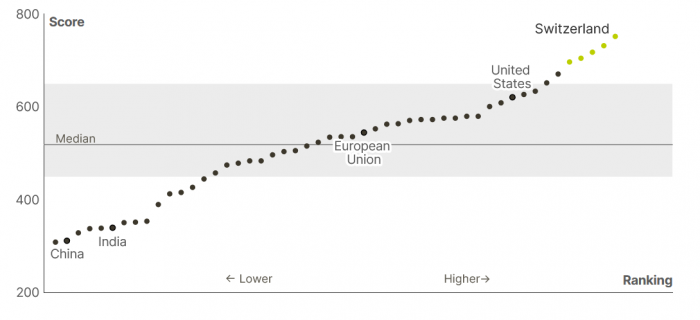
Cyber Security Education by Country World Economic Forum
This is precisely the kind of effort IT departments must put in today, especially knowing that hackers are increasingly creative with (how) they intrude upon intentional seclusion. Simply put, it is clear that today - end-to-end encryption, while solid, is merely one tool in the toolbox for organizations of all sizes.
All this will require a great deal of ongoing education paired with instituting policies meant to foster company-wide transparency - on top of the obvious - security. If there were ever an indicator of how important educating humans is, consider the following:
According to the World Economic Forum, a staggering 95 percent of cyber security breaches (are a result of) human error.



