The rise in remote work has helped increase team member productivity rates by close to 50%, drastically increased team employee satisfaction, and has even cut down on employee turnover rates.
Although managers may have initially worried about what employees would get up to on unsupervised company time, the surprising reality is that giving team members the ability to work from home offers far more benefits than many expected.
However, there is one major drawback to remote work: the potential for increased security threats and privacy issues that come when team members use their own devices and networks to access software, sensitive client data, and make/receive business phone calls.
Though VoIP features like call encryption, two-factor authentication, and call logs help to prevent or identify unusual activity, there are still security vulnerabilities and privacy pitfalls to watch out for -- especially when it comes to your behavior online.
Using a VPN for VoIP calling adds extra layers of protection and privacy that help both in-house and remote workers to stay secure. But what is a VPN, and how can using one increase business communications security?
Read on to find out.
Quick links:
- What is a VPN?
- The Benefits of VPN
- What To Look For In A VPN for VoIP Provider
- Top VoIP VPN Providers
- Other Ways To Boost VoIP Calling Security
- VoIP Over VPN FAQs
What is a VPN?
A VPN, or Virtual Private Network, is a security application that creates a tunnel between the Internet and the device you’re using to access it.
The tunnel hides your actual IP address from both your ISP (Internet Service Provider) and the websites you access, effectively allowing you to browse the Internet anonymously.
But how does a VPN actually work?
VPN networks are connected to hundreds, often thousands of different private servers all over the world. (You’re able to select your preferred VPN server location.)
When you use the Internet, the VPN redirects your IP address and requests through their own private servers, masking your true IP address, your current location, and other sensitive data. It encrypts your data so that you can’t be tracked online, offering not only privacy but, more importantly, better security.
VPNs use protocols -- different methods that allow your device to connect to the VPN servers -- to provide the best possible experience for your specific device and needs.
Note that proxy servers are not quite the same things as VPNs -- though many VPN providers also offer proxy servers as a feature.
Proxy servers also allow you to access the Internet on local routers or remote servers while appearing as though you’re in a different location than you really are. The difference is that web proxies only encrypt your web browser traffic -- whereas VPNs reroute and encrypt all of your Internet traffic and web activity, including downloads, online chats, games, and more. VPNs also work across multiple devices, whereas proxies will only work on the devices they’ve been configured on.
The Benefits of VPN
VPNs offer a whole host of benefits to both residential and business users.
First of all, a VPN lets users circumvent Internet access and usage restrictions, whether these restrictions are country-wide, school-wide, or even workplace-wide.
This not only means you’ll be able to access websites and online applications that may not be readily accessible in your country or specific building, but also that you’ll be able to leverage the power of VPN to get better shopping deals, shipping rates, and yes, even access to all those foreign television shows you love so much.
But while VPNs can be used recreationally, it’s what they can provide for your workplace and VoIP phone systems that really make a difference - especially given the advantages that Voice Over Internet Protocol phones offer over traditional landlines.
The Advantages of VoIP VPN
Given that it can take 228 days to even identify a data breach (let alone the 80 days needed to contain the breach) anything that you can do to secure your company’s data is invaluable.
VPNs can prevent website applications and sites from accessing your business VoIP and customer data, help you to escape pesky targeted ads, and ensure that hackers can’t access things like credit card information or account logins they could use to impersonate your company.
Additional VPN benefits include secure streaming and downloads, safer file sharing and team collaboration, and preventing DoS attacks, packet sniffing, and public Wi-Fi hacking attempts.
VoIP VPNs also allow businesses to unblock applications like Google Hangouts, Viber, Zoom, Skype, and other communications tools that may be geographically blocked in certain locations. VPNs also add extra layers of security to your business phone calls thanks to 256-bit encryption.
Plus, being able to choose your exact location helps you save serious money on international or long-distance calls.
Additional VPN VoIP calling benefits include:
- Higher voice call quality thanks to the prevention of bandwidth throttling
- Faster and more consistent service due to data throttling prevention
- Network scalability
- Allows remote team members to access business communication software securely from anywhere
What To Look For In A VPN for VoIP Provider
Before we get into the top VPNs for VoIP services, let’s quickly review what to look for in a quality service.
Large Server Network
The higher the number of servers your VPN provider has, the more geographic diversity you’ll be able to have.
Look for providers that offer a minimum of 1,000 IP servers in over 30 countries across multiple continents/regions.
Plus, the more servers the provider offers, the more likely it is that you’ll be able to find one that’s close to your true physical location -- an essential step when it comes to securing high speeds.
Data Encryption
Data encryption is the most important aspect of a VPN -- so you need to ensure your provider approaches encryption from several angles.
In a nutshell, encryption scrambles your sensitive data into meaningless strings of letters, numbers, and special characters so that even on the off chance that a hacker can access your accounts and data, they won’t be able to decipher and use them.
As a part of their encryption strategy, each provider should offer several different protocols.
These can often include:
- AES 256-bit encryption
- SSL (Secure Socket Layer) and TLS (Transport Layer Security)
- OpenVPN
- IKEv2/IPSec
- L2TP
- SSTP
A No-Log Policy
VPN providers should have strong no-log policies in place. Essentially, these policies make it clear that, although the VPN provider has access to some of your network’s data, they routinely delete it, don’t share or track it, and certainly don’t sell it.
Split Tunneling
Make sure your provider also offers split tunneling, which allows you to route a portion of your VoIP traffic through an encrypted VPN tunnel while allowing some other applications or devices to access the Internet without a VPN.
Why?
Because in many cases, you won’t be able to access both local and foreign Internet services simultaneously. Additionally, VPN data transmission can use up an excessive among of bandwidth.
Split tunneling ensures your Internet speed remains high, allows you to use local devices while securely browsing, and lets you access foreign websites while still accessing the local Internet.
High-Speed Connections
While it’s true that a VPN can sometimes slow down your Internet connection, high-quality providers will have workarounds to prevent a lag.
Make sure you ask your provider the specific steps they take to address potential latency and ensure your Internet speed is not negatively impacted by their VPN.
Kill Switch
The “Kill Switch” feature doesn’t just protect your team when it’s connected to the VPN. It also protects your privacy in the event of a disconnection from your Internet connection or a brief disconnect from the VPN service itself.
The Kill Switch effectively shuts off your ability to access the Internet and can block VoIP services until the connection has been re-established. It also ensures you’re not disconnected from the VPN when switching between devices.
Top VoIP VPN Providers
Below, we’ve reviewed some of the best VPN services for VoIP: ExpressVPN, NordVPN, and IPVanish VPN.
While ExpressVPN has only one type of subscription for both business and residential/recreational users, both NordVPN and IPVanish VPN offer business subscriptions. The provider that will work best for you depends on your specific needs, business size, and communications preferences.
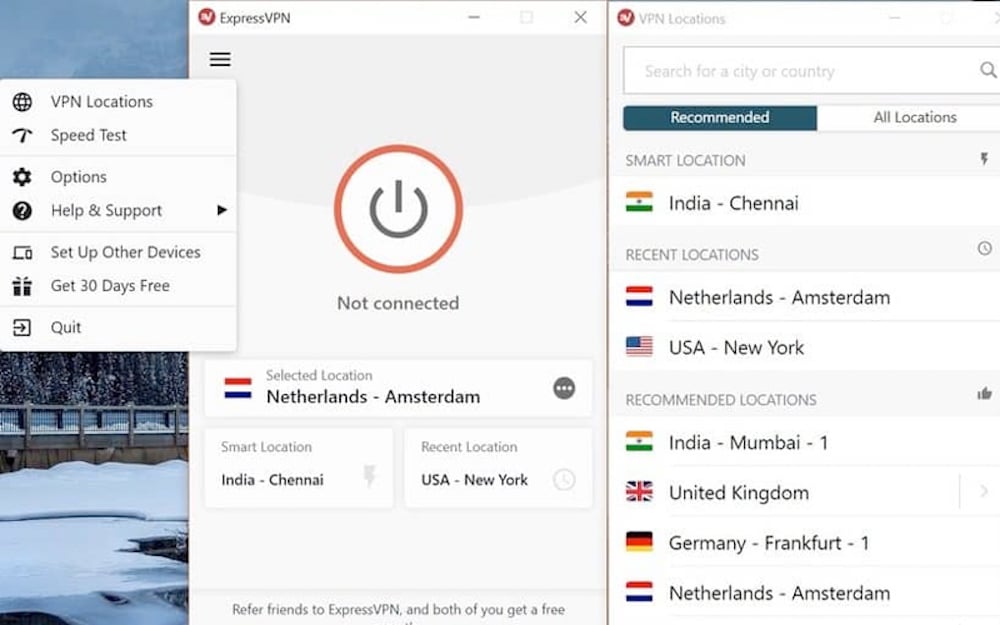
ExpressVPN
ExpressVPN is a VPN application with access to over 3,000 VPN servers in 160 different server locations within 94 countries. It is compatible with a wide variety of devices and web browsers in addition to a standard Internet router, including:
- Microsoft Windows and Apple Mac systems
- Android and iOS mobile devices
- Linux, Chromebook, Kindle Fire
- VPN browser extensions for Google Chrome, Firefox, and Edge
ExpressVPN even offers VPN services for smart TV systems like Roku and Apple TV, as well as gaming systems such as Xbox, Playstation, and Nintendo Switch (though of course, we know you’d never dream of accessing such things during work hours.)
It operates with AES-256 encryption, which offers virtually impenetrable protection against brute force attacks by ensuring that third parties like your ISP or Wi-Fi provider can’t intercept and read your activity as it travels from the VPN server to your device. Plus, ExpressVPN doesn’t simply mask your IP address -- it actually mixes your web traffic with the traffic of other users.
ExpressVPN also uses a variety of VPN protocols via its Lightway protocol tool.
Lightway uses the wolfSSL cryptography library to automatically determine the strongest encryption algorithm for your VoIP PBX system based on the strength of your current Internet connection. Lightway also helps prevent VPN from draining your device’s battery and speeds up the time it takes to connect to a VPN. And if you need to switch between VPN networks? Lightway will ensure you’re still connected to a VPN network during the entire process.
ExpressVPN never logs your IP address, (your VPN IP or source IP address) your browsing history, DNS queries, nor traffic destination/metadata.
Additional ExpressVPN benefits include:
- Unlimited bandwidth
- 30-day money-back guarantee
- Use your ExpressVPN account on up to 5 devices simultaneously
- Encrypted DNS
- TrustedServer Security (Data wiped with every reboot)
- VPN Split Tunneling
- VPN speed test
- Network Lock to block all Internet traffic until the VPN connection is restored
Users can choose from 3 subscription plans: A month-to-month plan for $12.95/month, a six-month plan for $9.99/month, and an annual plan for $8.32/month.
Best For: ExpressVPN is an ideal solution for businesses with a remote or blended workforce that’s geographically diverse. Team members that would benefit most from ExpressVPN also switch devices throughout the day and rely on several devices that operate via the Internet of Things (IoT) Finally, it’s an excellent option for companies prioritizing ease of installation, as the setup takes just under five minutes and is highly user-friendly.
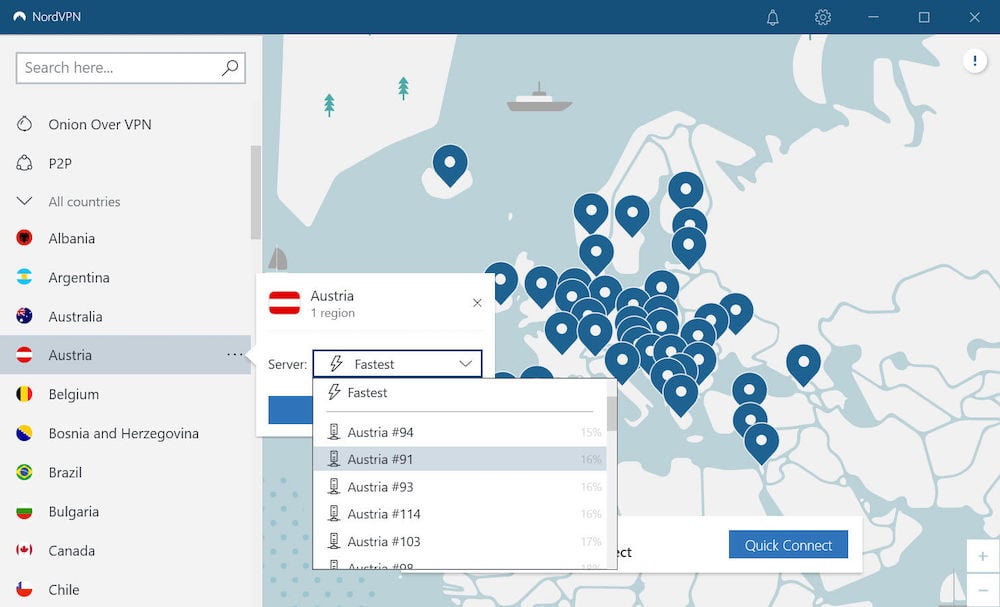
NordVPN
NordVPN is a VPN service provider available for macOS, iOS, Android, and Windows devices with over 5,300 servers in 59 countries.
NordVPN also offers a business VPN solution, NordVPN Teams, that’s especially ideal for VoIP phone service and SMBs. The Teams plan offers centralized billing, a dedicated account manager, and the ability to control permissions and create gateways within the Teams control panel.
It uses three main VPN protocols: IKEv2/IPSec, OpenVPN, and NordLynx to ensure you have access to the latest cryptography developments. It even offers obfuscated serves, which prevents your ISP from seeing you’re using a VPN. Dedicated IP addresses are available, and the CyberSec tool automatically blocks suspicious websites that commonly host phishing scams or simply feature too many obnoxious pop-ups.
You can also access Onion Over VPN for even more privacy, or enjoy the Nord VPN “Double VPN” tool -- which routes your data through not one, but two different VPN servers.
As your business grows, you’re also able to add on dedicated servers, create custom teams with their own gateways, select team IP address location, and monitor your current server load. Each NordVPN account lets users secure up to six simultaneous devices, and there are no bandwidth caps.
Additionally, NordVPN is a no-log service, meaning they don’t store information about your IP addresses, bandwidth usage, traffic, timestamps, and session data. Their no-log policy has been verified by PWC for added security.
NordVPN also offers:
- AES 256-bit encryption
- Two-factor authentication via Google Authenticator and Authy
- Kill Switch to prevent unprotected Internet access in the event of a connection loss
- Third-party login via Azure AD, Google, or Okta
- Team license transferability
- Split tunneling
- Encrypted proxy extensions for Chrome and Firefox
- A 30-day money-back guarantee
- Hardwall firewalls
Users can choose from three available paid standard plans: a month-to-month plan for $11.95/user per month, a one-year plan for $6.58/user per month, or a two-year plan for $4.13/user per month. Three NordVPN Teams subscriptions are also available: The quote-based Enterprise Plan, the Advanced Plan for $9.00/user per month, and the Basic Plan for $7.00/user per month.
Best For: NordVPN is best for companies that need an advanced level of VoIP with SIP and military-grade cybersecurity, likely because they work within industries with either strict compliance regulations or a large amount of personal data. It’s also ideal for smaller remote teams and startups that access public Wi-Fi regularly.
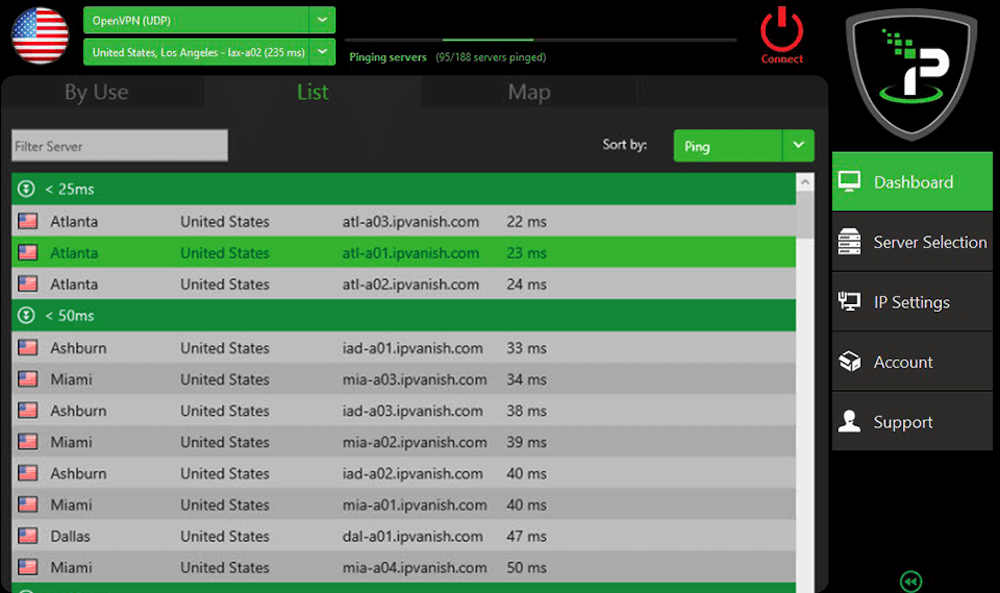
IPVanish VPN
IPVanish VPN is a VPN with servers more than 40,000 shared IPs from 1,600 servers in over 75 regions worldwide, unmetered device connections, and no data transfer caps.
It’s compatible with:
- Windows and macOS
- Android and iOS
- Chrome and Linux
- Fire TV
It offers several VPN protocols, including IKEv2. IKEv2 configures the strongest possible approach to IP packet encryption and allows users to switch between mobile and Wi-Fi networks without disconnecting the VPN.
Users can also access the OpenVPN protocol, which uses SSL and TLS for authentication and key exchanges.
Additional benefits include:
- L2TP (Layer 2 Tunneling Protocol) for mobile devices
- Ability to share IP addresses with other users for increased security
- IPSec protocol suite to encrypt IP packets for tunneling and transport
- Zero traffic logs
- SOCKS5 Proxy web server
IPVanish VPN lets users choose between a standalone VPN or a VPN and secure storage bundle.
Standalone IPVanish VPN is available with a month-to-month plan ($3.49/the first month, $9.99/month afterward) or an annual plan ($2.62/month for the first year, $89.99/year afterward.) The VPN and storage combination offers up to 500 GB of storage in addition to VPN protection. Users can choose between the monthly combination plan ($3.84/the first month, $10.99/month afterward) or the annual combination plan ($2.92/month for the first year, $99.99/years afterward.)
IPVanish VPN also offers Encrypt.me, a team-based enterprise solution for businesses needing VoIP VPN calling. Plans are available from $7.99/user per month. Encrypt.me features include:
- Private Endpoints ($15.00/endpoint) with a static IP address
- Content Filtering that lets admins block distracting or suspicious, potentially dangerous websites
- SugarSync file storage with encrypted backup scheduling, protected folders/file recovery, and secure file sharing
Best For: IPVanish VPN is best for enterprise-level teams that need not only VPN protection for team members but also secure data storage solutions. It’s also ideal for teams of any size that use a high number of different devices every day, and need to be able to run their VPN services on an unlimited number of devices.
Other Ways To Boost VoIP Calling Security
Though installing a VPN for VoIP calls is an excellent way to protect your privacy, there are additional steps you can take to improve your virtual phone service security for both clients and employees.
Create a strong company password policy and outline clear regulations for personal online communication and web browsing during work hours. Add firewalls, use anti-virus software, and turn on automatic updates for your VoIP system to ensure that you’re protected against the latest cyber-attacks.
Also use two-factor authentication, spam call blockers, and call screening tools.
VoIP Over VPN FAQs
Below, we’ve answered some of the most common questions about VPNs.